- DATE:
- AUTHOR:
- The Stytch team
2022.11.18 release
Device Fingerprinting
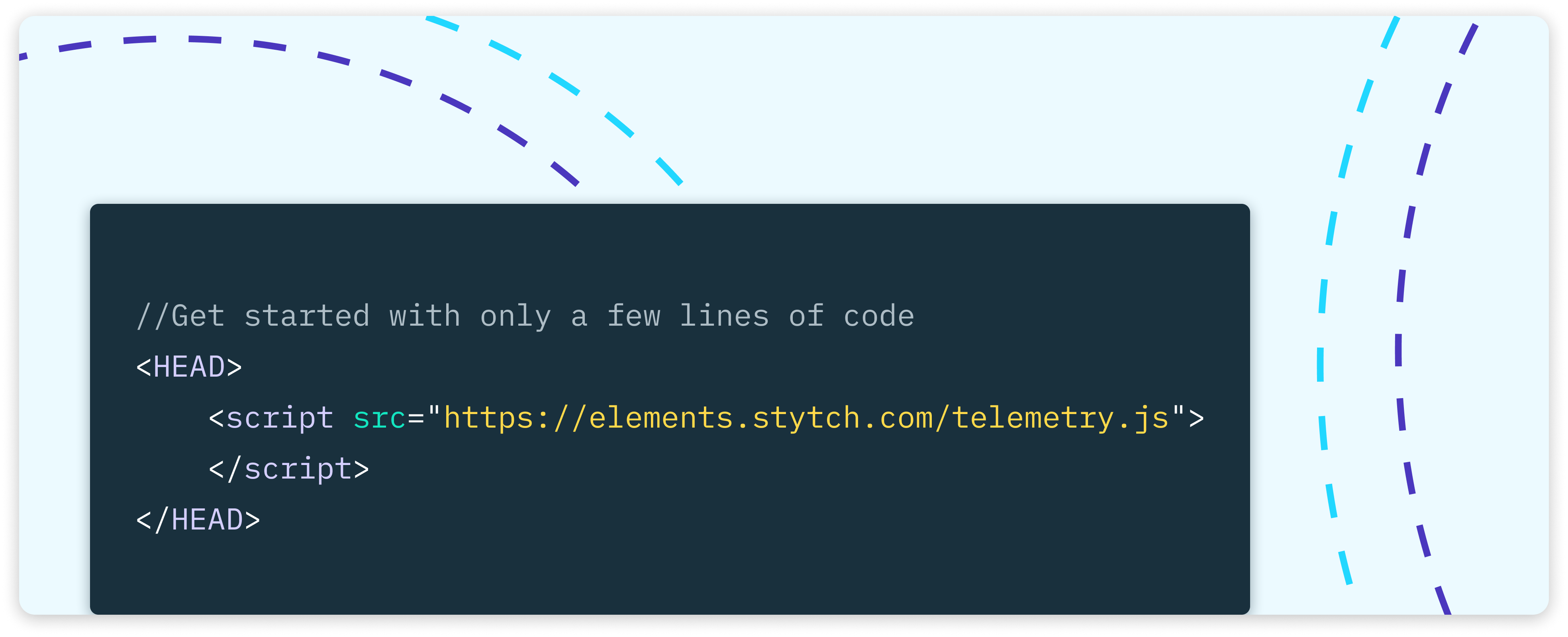
We’re excited to announce Device Fingerprinting, a set of customizable tools to identify and evaluate the characteristics of devices for fraud prevention and fine-grain traffic shaping. Stytch’s device fingerprints remain accurate even when a device switches across incognito browsing, webviews, VPNs, user agents, IP addresses, and more.
Use Device Fingerprinting to:
Determine whether a device is an actual physical device or a bot attack attempting to spoof real device-based traffic.
Prompt bad actors to complete a CAPTCHA or block them entirely.
Force multi-factor authentication if you’ve never seen the device before.
Customize the experience for an anonymous visit to your site without introducing login friction.
Prevent account takeover and sharing.
Globally unique IDs
Every device you fingerprint generates a unique identifier you can leverage to create granular controls within your auth flows.
Device classification grouping
Stytch automatically classifies device fingerprints into categories based on the level of trust (i.e. likelihood that it is a bot or malicious traffic).
Actions
Stytch provides three default suggested actions – Allow, Block, and Challenge – for each device grouping or unique device ID.
Check out the docs here and talk to an auth expert to get started.
“For engineers”
We launched a new “For engineers” category on our blog where we’ll share how our engineering team solves and thinks about technical challenges. At Stytch, we’re focused on building great developer experiences – not just for our customers but for our own team as well.
Learn how an early choice to build a fully remote dev environment has paid dividends. Read more about it here.